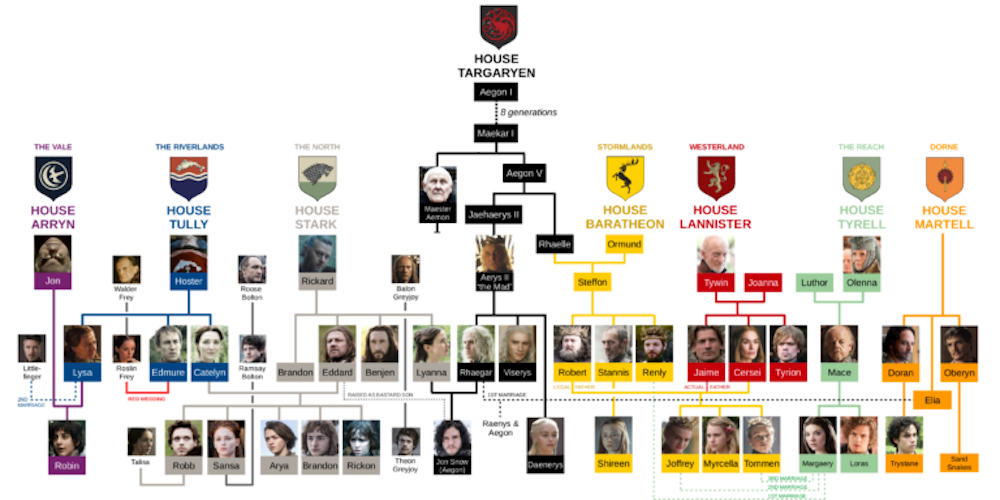
If you’ve ever spent any amount of time delving into the world of Common Criteria (CC), you’ve no doubt come across the veritable Roman/biblical hierarchy of relationships between the various components. At times, it would make even Cersei Lannister blush. In support of the CC automation we are doing at Lightship Security, I took on the daunting task of modelling this complex family tree in software. Here’s what I learned about who begat whom in the family tree of CC requirements.
Read MoreOttawa’s Fastest Growing Companies – #2 for 2019
Lightship Security has been named as Ottawa’s second Fastest Growing Company for 2019.
Every year the Ottawa Business Journal (OBJ) recognizes 10 regional companies for their substantial, sustainable, and profitable growth.
Fueled by an industry first automated approach to product security certification, we have bootstrapped our way to substantial growth over a three-year period to earn the 2019 award.
Lightship’s mission to modernize the legacy approach to 3rd party product security certifications (like Common Criteria) through our automated test platform, Greenlight is proving a key differentiator and driver of sales growth. Our approach dramatically eliminates the risk of certification delays, product re-development and reduces time to market for a growing list of international clients.
Read MoreUnderstanding the Scope of NDcPP Evaluations
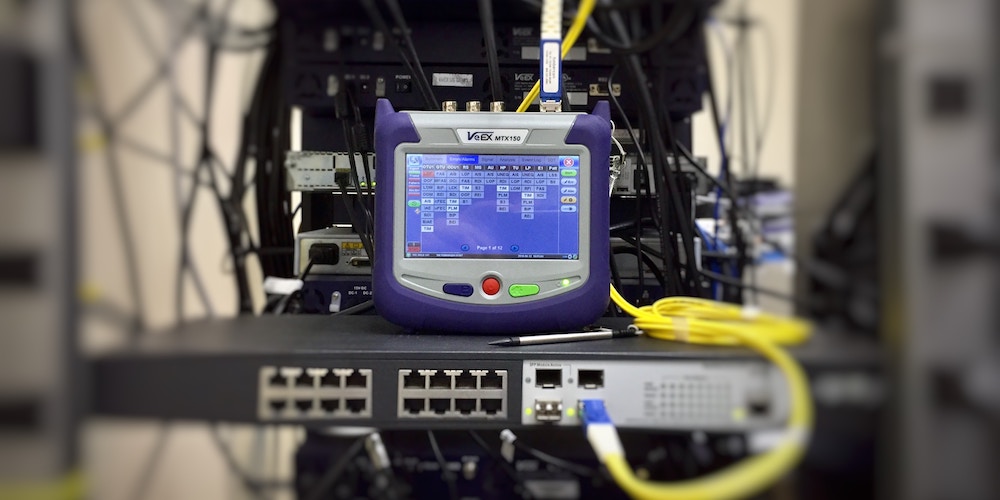
When first exposed to the Network Device collaborative Protection Profile (NDcPP), vendors are often surprised by the extremely narrow scope. It is critical to realize that the Protection Profile (PP) refers to an abstract “network device” with required functionality that should appear in any good network citizen. It doesn’t look to any specific vendor or technology type. Rather, the PP refers to the minimalist ideal of security-relevant functionality focused almost entirely on how security administrators interface and interact with the device.
Read MoreChallenges in Fuzzing RFC 1149
Conan Hoye and Greg McLearn contributed to this article.
At Lightship, we test a lot of NDcPP-compliant products. As part of those evaluations, we are required, as per Appendix A in the Supporting Document, to perform network fuzzing against the in-scope IP networking stacks. Recently we had a rather unique TOE which claimed conformance against RFC 1149 for one of their remote management interfaces.
Read MorePreparing for FIPS Validation Part 2 – Boundaries and Libraries
In part 2 of our multi-part Lightship Security video tutorial series geared toward vendors who are new to FIPS 140-2, we discuss the concept of cryptographic boundaries, cryptographic libraries and the design aspects required for FIPS 140-2 compliance. The previously published part 1 of the series can be found here.
Read MoreNDcPP v2.1 endorsed by NIAP but which TDs apply?
NIAP announced their endorsement today of version 2.1 of the Network Device collaborative Protection Profile. We’ve previously described the changes in NDcPP v2.1. In this post, we look at which NIAP Technical Decisions (i.e. interpretations / minor edits) will still apply to this new version.
Read MoreNDcPP – Are You A Good Network Citizen?
Vendors undertaking a Common Criteria project for the first time are often surprised by the scope and focus of the testing for a Network Devices collaborative Protection Profile (NDcPP) CC evaluation. Lightship’s Technical Director, Greg McLearn often refers to the testing involved in the NDcPP as “ensuring that the product is a good network citizen”. This is the NDcPP philosophy.
Read MoreWhat’s changed since NDcPP v1.0?
There are 41 products listed on the NIAP PCL that are compliant with the collaborative Protection Profile for Network Devices (NDcPP) v1.0. These PCL listings will all expire within the next year or so. What can these vendors expect when updating their certifications from NDcPP v1.0 to NDcPP v2.0e? In this post, we examine the changes that have occurred to the NDcPP to help answer this question.Read More
Preparing for FIPS Validation – Common Pitfalls
In this multi-part Lightship Security video tutorial series geared toward vendors who are new to FIPS 140-2, we discuss the “origins” of a cryptographic module and the design requirements for FIPS 140-2 compliance. The tutorial also touches on self-tests and the concept of FIPS 140-2 “modes of operation” including Approved, non-Approved, and Mixed Modes. Stay tuned for further installments.
Read MoreWelcome to the NIAP TLS 1.1 Functional Package
Edit 20-March-2019: NIAP published a v1.1 of the Functional Package which addresses many of the item discussed in this blog. The title of the blog is updated and ambiguities previously found are corrected where they’ve been addressed.
NIAP recently released their first, and widely anticipated, modular protection profile package targeting the TLS communication protocol. This package is not meant to stand on its own and is designed to be included within new versions of NIAP protection profiles. While it is unlikely to be explicitly referenced by collaborative Protection Profiles (cPP), the requirements will almost certainly be highly similar.
Read More