A Practical Guide for Security, Engineering, and Compliance Teams
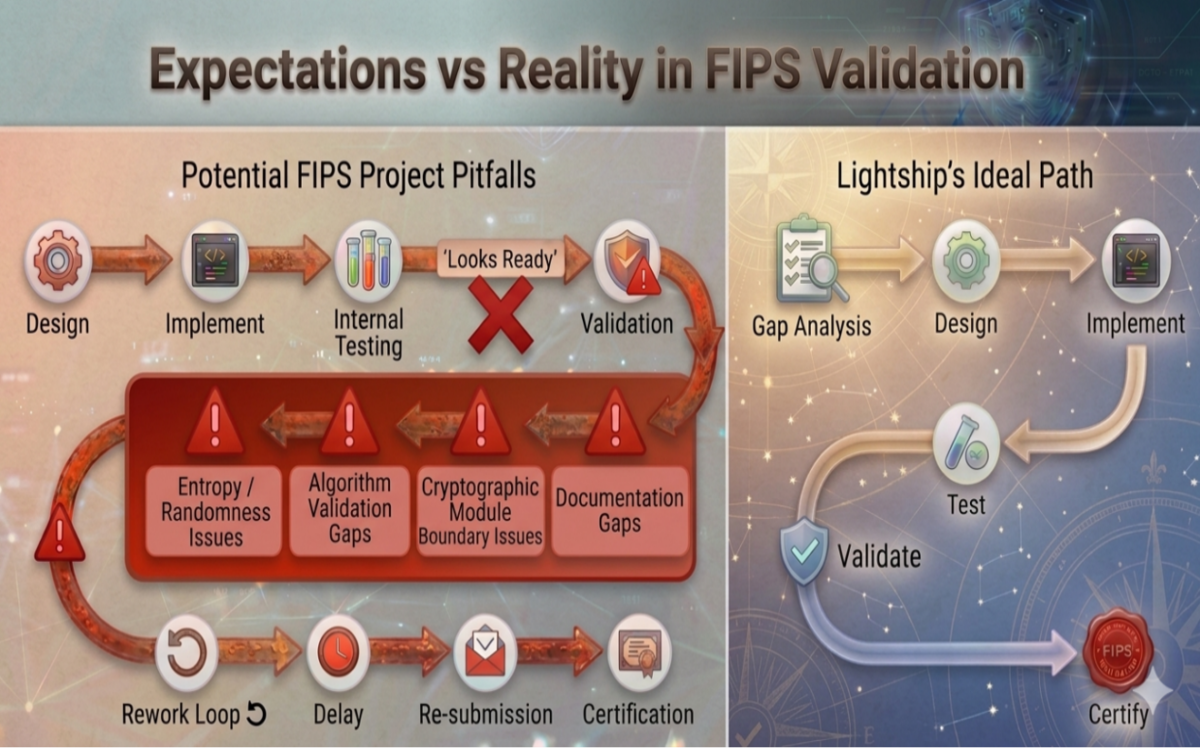
Achieving FIPS validation is often viewed as a final checkpoint—something to address once development is complete. In practice, this mindset is one of the most common reasons organizations encounter delays, rework, and unexpected certification challenges.
FIPS validation is not simply a test passed at the end of development. It is a rigorous evaluation of cryptographic design, implementation, architecture, and documentation. Understanding how the process really works—and where projects often go wrong—can make the difference between a smooth validation and months of delay.
Read More